Connecting state and local government leaders
Safeguarding an agency against email compromise involves both administrative awareness and technical controls, such as email rules, filtering and third-party solutions.
Business email compromise (also known as “CEO fraud” or the “man in the middle” scheme) is an attack that tricks an individual into transferring money to a criminal’s bank account in response to an email that seems legitimate to the recipient. This scheme affects consumers, business and government agencies -- any entity that transfers money online. To date, more than $3 billion in actual and attempted losses have been reported.
According to the FBI, there are five common forms of BEC in which criminals:
- Masquerade as trusted contractors so the request for funds seems legitimate.
- Spoof or hack the email accounts of executives so the authority for the transfer seems to be from senior management.
- Hack an employee’s email account to send fraudulent invoices to contractors.
- Masquerade as an attorney handling urgent or confidential transactions to pressure recipients into action.
- Spoof requests for sensitive employee information that can be used for identity theft or network compromise.
In the first four scenarios, the sender pretends to be in a position of trust or authority. The fraudster tenders a seemingly legitimate request for the transfer of funds to a criminally controlled account. The unwitting recipient will then wire the requested funds to that account.
In the fifth scenario, the fraudster may masquerade as an IRS employee or other entity in the tax industry to obtain W2 or other personally identifiable information of employees that can be used for identity theft and tax fraud purposes.
Fraudsters may easily find information about potential targets through social media and websites, including job titles, duties, descriptions, hierarchical information and out of office information. A fraudster may connect with or befriend the target on social media -- potentially masquerading as someone else -- to collect more information, either passively or by actively soliciting information. Fraudsters may especially be interested in locating individuals who are responsible for handling wire transfers within the organization.
What BEC Looks Like
The FBI offers the following BEC example in which a fraudster is masquerading as the CEO:
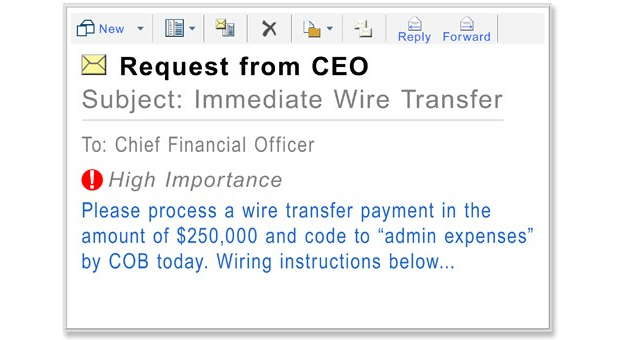
Recipients should flag suspicious communications from a sender’s email account they do not recognize, an odd URL, an unusual sum of money, a change in wiring instructions (including routing and account numbers), a change in wire transfer procedure, or anything else that may seem out of the ordinary.
If the request appears to be unusual, consider conducting additional due diligence on the requested transaction and verify the request using an out-of-band communication method, such as by telephone (or, better yet, in person, if possible) -- consistent with the organization's policy. Additionally, management should be informed of suspect emails immediately.
BEC incidents may also be reported to the local FBI or Secret Service field office or the Internet Crime Complaint Center. Additional information on potential BEC red flags is available from the Treasury Department, which notes in its advisory that financial institutions may be obligated to file a suspicious activity report with the Financial Crimes Enforcement Network.
Mitigating BEC
Safeguarding an agency against BEC involves both administrative (e.g., policies, awareness, etc.) and technical controls, such as email rules, filtering and vendor solutions. Some practical tips include the following:
- Educate all workforce members on BEC.
- Flag internal vs. external emails.
- Consider creating an organizationwide BEC policy (including what BEC is, what to do, who to report to, etc.).
- Share with care on social media, especially information related to job functions, titles, etc.
- Consider using two-factor authentication for wire-transfer requests.
- Take additional measures to verify or confirm any suspicious request.
Business email compromise is a growing threat that can be very damaging (and costly) to victim organizations. Increased awareness, education and appropriate policies and procedures are the quintessential elements that are necessary to thwart scams such as BEC.
NEXT STORY: Why threat-data sharing is so hard



