Derived credentials for mobile on the horizon?
A recently announced partnership between MobileIron and Entrust Datacard aims to deliver a derived credential solution by the end of the year.
Can users help solve the mobile security disconnect?
Today’s mobile IT environment -- with all of the issues bring-your-own-device policies and shadow IT mobile bring with it -- represents a starkly different world to secure and manage.
NIST drafts mobile security guidelines for responder tech
The National Institute of Standards and Technology’s reference design would improve interoperability between mobile platforms, applications and identity systems for public safety organizations.
Critical infrastructure in the crosshairs
Protecting the infrastructure from attack will require a new way of thinking about critical systems cybersecurity.
No such thing as a benign app?
Now that hackers use apps as a front end for their attacks, ‘benign’ no longer means what you think it does.
The bad news about bug hunting
The Pentagon's recent pilot program shows just how pervasive the exploitable network vulnerabilities are.
Software-defined perimeter security for cloud-based infrastructures
A recent demonstration tested the viability of using an SDP front end to provide the access between various compute resources located across multiple public clouds.
Is predictive analytics really a game changer?
It may be too soon to tell, but predictive analytics offers agencies hope that they can get ahead of the threat rather than just cleaning up after the fact.
Prep for next-gen encryption should start yesterday
Because the effort to pull together any kind of quantum-resistant cryptography will be lengthy and complex, the process must start now if those trusted cryptosystems are to be developed in time.
Confidence: The secret sauce for security
When neither employers nor workers have confidence in an organization’s ability to protect data, security tools can only provide part of the answer.
Government slow to mount defense against APTs
The FBI believes at least one group of hackers has been using APTs against government agencies for at least the past five years -- and possibly much longer.
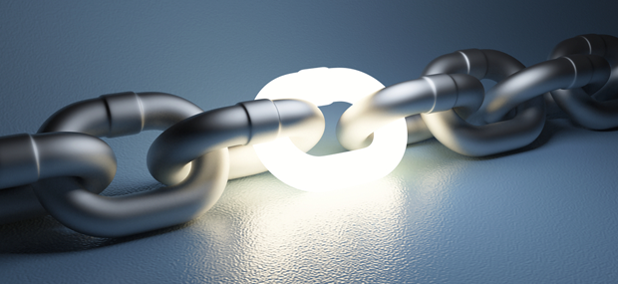
How blockchain works
A blockchain-based system marries ironclad trust to a fully auditable sequence of digital events enclosed in a highly secure environment.
Secure code before or after sharing?
When agencies release code to open source, should they sanitize it before release or trust to the community to eventually secure it?
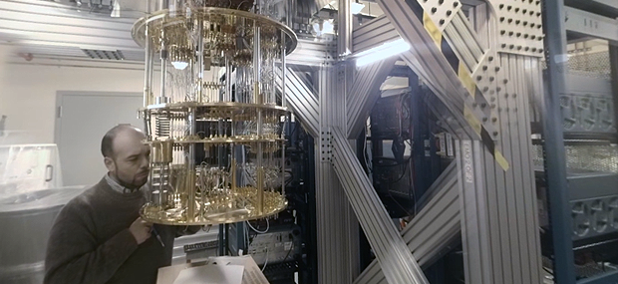
Can we build quantum-resistant encryption?
New research demonstrating that quantum computing is now just an engineering challenge moves the possibility of encryption-cracking machines to the front burner.
Feds want mobile security, except when they don’t
Conflicting messages over mobile devices security sow doubt and confusion.
Is SDx the model for IT security?
Software-defined systems could prove the best way to tackle the security problems that otherwise threaten to overwhelm government.
Still early days for federal cybersecurity?
While Congress seems to understand the urgency of implementing cybersecurity solutions, critical technology that was recognized as essential years ago still isn’t fully deployed.
Heartbleed redux with Secure Shell?
Warning flags have been raised over SSH, which helps manage servers, routers and firewalls and is used to provide privileged access to servers and networks.
Cybersecurity in 2016: Real change or more of the same?
Despite 2015 providing an embarrassment of cybersecurity breach riches, there’s not much indication that government overall is paying that much more attention to security.
Why network resiliency is so hard to get right
Both perimeter defense and effective elimination of threats that have breached the network are key components of a cybersecurity strategy. But what's the right mix?
Do Not Sell My Personal Information
When you visit our website, we store cookies on your browser to collect information. The information collected might relate to you, your preferences or your device, and is mostly used to make the site work as you expect it to and to provide a more personalized web experience. However, you can choose not to allow certain types of cookies, which may impact your experience of the site and the services we are able to offer. Click on the different category headings to find out more and change our default settings according to your preference. You cannot opt-out of our First Party Strictly Necessary Cookies as they are deployed in order to ensure the proper functioning of our website (such as prompting the cookie banner and remembering your settings, to log into your account, to redirect you when you log out, etc.). For more information about the First and Third Party Cookies used please follow this link.
Manage Consent Preferences
Strictly Necessary Cookies - Always Active
We do not allow you to opt-out of our certain cookies, as they are necessary to ensure the proper functioning of our website (such as prompting our cookie banner and remembering your privacy choices) and/or to monitor site performance. These cookies are not used in a way that constitutes a “sale” of your data under the CCPA. You can set your browser to block or alert you about these cookies, but some parts of the site will not work as intended if you do so. You can usually find these settings in the Options or Preferences menu of your browser. Visit www.allaboutcookies.org to learn more.
Sale of Personal Data, Targeting & Social Media Cookies
Under the California Consumer Privacy Act, you have the right to opt-out of the sale of your personal information to third parties. These cookies collect information for analytics and to personalize your experience with targeted ads. You may exercise your right to opt out of the sale of personal information by using this toggle switch. If you opt out we will not be able to offer you personalised ads and will not hand over your personal information to any third parties. Additionally, you may contact our legal department for further clarification about your rights as a California consumer by using this Exercise My Rights link
If you have enabled privacy controls on your browser (such as a plugin), we have to take that as a valid request to opt-out. Therefore we would not be able to track your activity through the web. This may affect our ability to personalize ads according to your preferences.
Targeting cookies may be set through our site by our advertising partners. They may be used by those companies to build a profile of your interests and show you relevant adverts on other sites. They do not store directly personal information, but are based on uniquely identifying your browser and internet device. If you do not allow these cookies, you will experience less targeted advertising.
Social media cookies are set by a range of social media services that we have added to the site to enable you to share our content with your friends and networks. They are capable of tracking your browser across other sites and building up a profile of your interests. This may impact the content and messages you see on other websites you visit. If you do not allow these cookies you may not be able to use or see these sharing tools.
If you want to opt out of all of our lead reports and lists, please submit a privacy request at our Do Not Sell page.
Cookie List
A cookie is a small piece of data (text file) that a website – when visited by a user – asks your browser to store on your device in order to remember information about you, such as your language preference or login information. Those cookies are set by us and called first-party cookies. We also use third-party cookies – which are cookies from a domain different than the domain of the website you are visiting – for our advertising and marketing efforts. More specifically, we use cookies and other tracking technologies for the following purposes:
Strictly Necessary Cookies
We do not allow you to opt-out of our certain cookies, as they are necessary to ensure the proper functioning of our website (such as prompting our cookie banner and remembering your privacy choices) and/or to monitor site performance. These cookies are not used in a way that constitutes a “sale” of your data under the CCPA. You can set your browser to block or alert you about these cookies, but some parts of the site will not work as intended if you do so. You can usually find these settings in the Options or Preferences menu of your browser. Visit www.allaboutcookies.org to learn more.
Functional Cookies
We do not allow you to opt-out of our certain cookies, as they are necessary to ensure the proper functioning of our website (such as prompting our cookie banner and remembering your privacy choices) and/or to monitor site performance. These cookies are not used in a way that constitutes a “sale” of your data under the CCPA. You can set your browser to block or alert you about these cookies, but some parts of the site will not work as intended if you do so. You can usually find these settings in the Options or Preferences menu of your browser. Visit www.allaboutcookies.org to learn more.
Performance Cookies
We do not allow you to opt-out of our certain cookies, as they are necessary to ensure the proper functioning of our website (such as prompting our cookie banner and remembering your privacy choices) and/or to monitor site performance. These cookies are not used in a way that constitutes a “sale” of your data under the CCPA. You can set your browser to block or alert you about these cookies, but some parts of the site will not work as intended if you do so. You can usually find these settings in the Options or Preferences menu of your browser. Visit www.allaboutcookies.org to learn more.
Sale of Personal Data
We also use cookies to personalize your experience on our websites, including by determining the most relevant content and advertisements to show you, and to monitor site traffic and performance, so that we may improve our websites and your experience. You may opt out of our use of such cookies (and the associated “sale” of your Personal Information) by using this toggle switch. You will still see some advertising, regardless of your selection. Because we do not track you across different devices, browsers and GEMG properties, your selection will take effect only on this browser, this device and this website.
Social Media Cookies
We also use cookies to personalize your experience on our websites, including by determining the most relevant content and advertisements to show you, and to monitor site traffic and performance, so that we may improve our websites and your experience. You may opt out of our use of such cookies (and the associated “sale” of your Personal Information) by using this toggle switch. You will still see some advertising, regardless of your selection. Because we do not track you across different devices, browsers and GEMG properties, your selection will take effect only on this browser, this device and this website.
Targeting Cookies
We also use cookies to personalize your experience on our websites, including by determining the most relevant content and advertisements to show you, and to monitor site traffic and performance, so that we may improve our websites and your experience. You may opt out of our use of such cookies (and the associated “sale” of your Personal Information) by using this toggle switch. You will still see some advertising, regardless of your selection. Because we do not track you across different devices, browsers and GEMG properties, your selection will take effect only on this browser, this device and this website.
Help us tailor content specifically for you: